Build your ISMS in minutes, not months.
.svg)
.svg)
.svg)
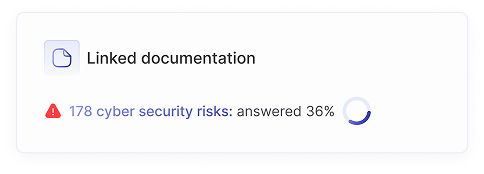
Discover comprehensive resources, expert insights, and proven strategies to identify, assess, and mitigate cybersecurity risks across your organization.
.png)



Clear, practical explanation of information security risk management, how it connects to security frameworks, and how to make risk-based security work in practice.


An ISMS only supports risk management if it’s actively used. When processes like incident management, change management, continuity planning, and continuous improvement are run in practice, they continuously generate input.


Find the 10 most common failures in information security risk management and learn how teams can fix them to make risk management practical, decision-driven, and effective in everyday security work.


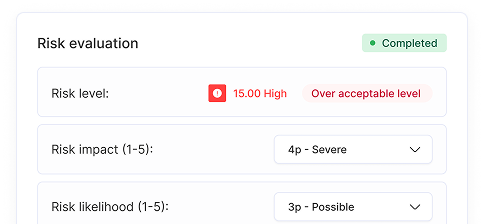
Clear, practical explanation of information security risk management, how it connects to security frameworks, and how to make risk-based security work in practice.


Learn why information security risk management is important. Discover how a risk-based approach helps optimize security, support compliance like ISO 27001, enable continuous improvement, and build risk-aware teams.


Manage information security risks with a clear step-by-step process, from asset identification to monitoring, essential for navigating growing cybersecurity threats.


We're constatly searching for ways to automate and create efficient cyber risk management. Our newest additions is risk autopilot mode. It's concept is described on this post.
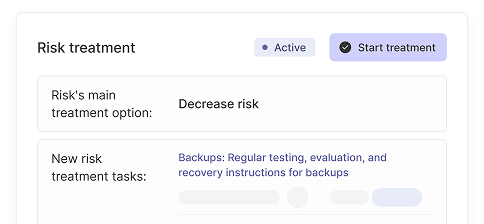
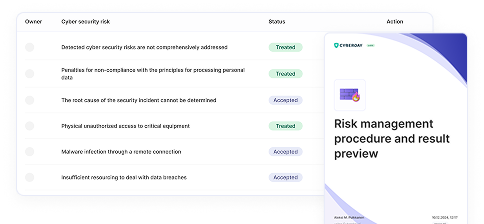
Cyberday transforms risk management into a living, breathing part of your security program, automatically updating as threats evolve and your organization grows.







