.png)
Workflows are a clearer way to find everything related to one theme - risks, awareness, incidents, assets - on a hub, with the metrics that matter and the documentation / tasks / reports you need.
Achieve continuous, evergreen resilience with a long-term ISMS solution, not just a one-off project. Simplify and speed up your compliance work with Cyberday AI Agents.
Cyberday gives you the clearest, most practical way to security compliance. Build structure, stay on top of requirements, and keep compliance running continuously. Start free in minutes.
.png)
For every stage of the journey
Whether you're picking the first requirements or scaling across a dozen frameworks or teams, Cyberday meets you where you are.
Security has been on someone's mind, maybe in a spreadsheet, maybe nowhere at all. Now there’s a deal on the line, NIS2 deadline, or maybe first customer asking for prove. Cyberday’s Fast Track reads your company profile and generates the baseline. Don’t start with nothing, see what you already have.
.png)
Replace scattered AI-generated or manual documents, spreadsheets, and Sharepoint silos with a single systematic overview of what needs to be done and who is responsible. Bring in what you have & AI can help you read it, map it, and tell you exactly where the quick wins are hiding.
.png)
Subsidiaries, business units, client accounts. Each with their own requirements, some shared, some not. Cyberday gives you layered governance: central control where you need it, local ownership where you don't.
.png)

Our AI tool analyzes your business, size, industry, tech stack and risks and builds your initial security profile automatically.
No forms, no 40-question onboarding. You start with something that already feels like you.
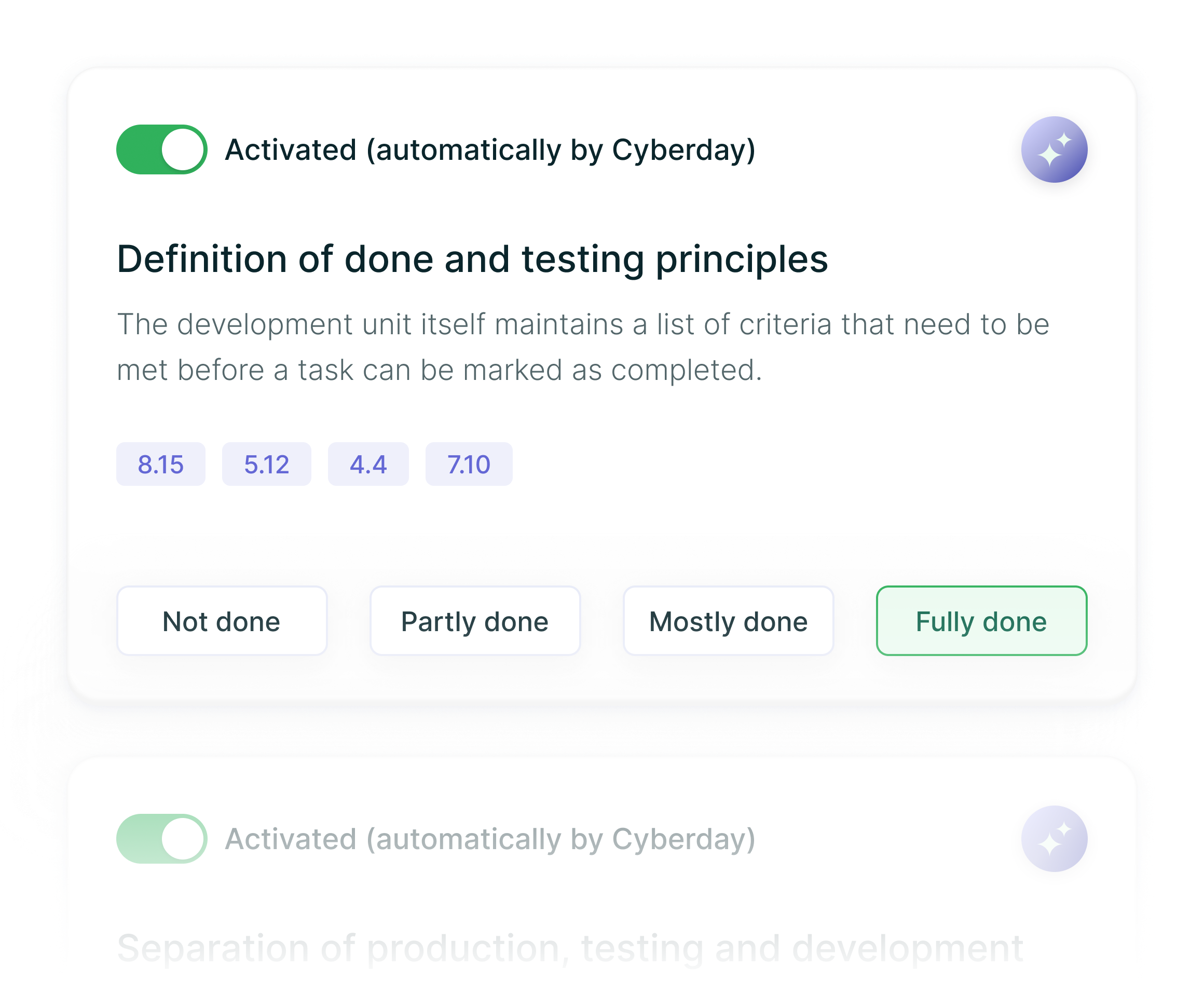
Based on your profile, AI activates the right framework (ISO 27001, NIS2, etc.) and generates a tailored compliance plan.
Clear. Prioritized. No guesswork. You instantly see what matters first and what can wait.
AI drafts your security policies and documentation using best practices — or from your own uploaded material.
Everything comes pre-filled with correct terminology, scope and responsibilities. You just review and approve.

Cyberday helps organizations who want information security management that actually works in practice, not just on paper.
Cyberday gave us the structure, the support, and the direction. Without it, we'd probably still be piecing things together in Google Drive.
Mikael Lavi
DPO at Ellie Technologies
.png)
.png)
.png)
Get a weekly digest with most important cybersec news, new Academy content and next week's free webinars.
Tiimimme seuraa jatkuvasti kymmeniä uutislähteitä maailmalta ja toimittaa tärkeimmät digiturvauutiset sähköpostiisi viikottain.








