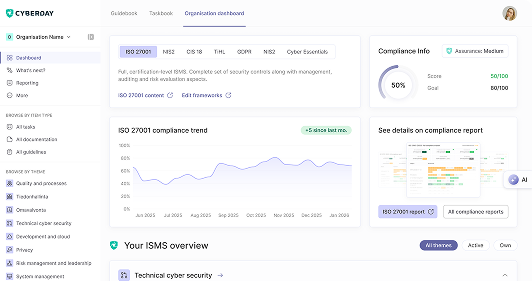
Build your ISMS in minutes, not months.
.svg)
Generate your ISMS baseline instantly with FastTrack
.svg)
Access the most extensive framework library on the market
.svg)
Try all features free for 14 days - no credit card needed.

The Netherlands’ Cyberbeveiligingswet imposes NIS2 obligations on essential and important entities, including risk management measures, ICT incident reporting, and supply chain risk assessments. Take the NIS2 Netherlands assessment to understand your obligations under the Cbw.



Vaatimukset täyttyvät jalkauttamalla digiturvatehtäviä.
Mitä kukin tekee digiturvan eteen?
Osa tehtävistä vaatii asioiden ohjeistamista henkilöstölle.
Mitä pitää muistaa arjessa?
Osa tehtävistä vaatii listausten pitoa tietoturvan ydinelementeistä.
Mistä pitää voida raportoida?