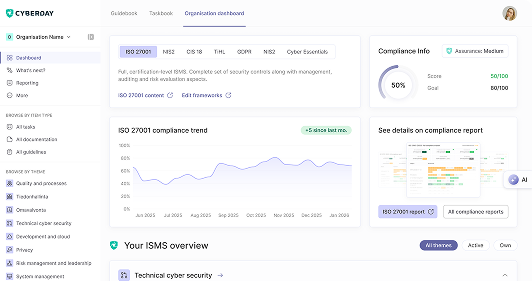
Build your ISMS in minutes, not months.
.svg)
.svg)
.svg)

CIS Controls 18 is a prioritized, comprehensive set of cybersecurity best practices covering vulnerability management, secure configuration, access control, incident response, and more. Start the CIS 18 assessment to benchmark your security posture against the controls and find out where you have gaps.



Vaatimukset täyttyvät jalkauttamalla digiturvatehtäviä.
Mitä kukin tekee digiturvan eteen?
Osa tehtävistä vaatii asioiden ohjeistamista henkilöstölle.
Mitä pitää muistaa arjessa?
Osa tehtävistä vaatii listausten pitoa tietoturvan ydinelementeistä.
Mistä pitää voida raportoida?