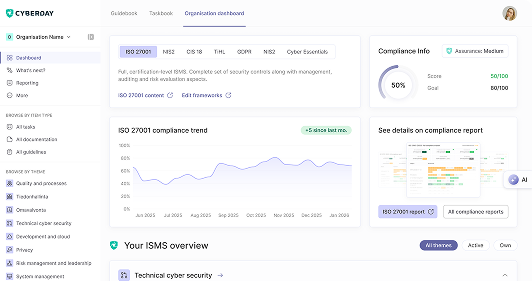
Build your ISMS in minutes, not months.
.svg)
.svg)
.svg)

Lithuania's Description of Cybersecurity Requirements defines the organizational and technical measures for NIS2-scope entities, covering employee training, incident management, business continuity planning, and third-party security. Check your compliance posture with the NIS2 Guide Lithuania assessment.



Vaatimukset täyttyvät jalkauttamalla digiturvatehtäviä.
Mitä kukin tekee digiturvan eteen?
Osa tehtävistä vaatii asioiden ohjeistamista henkilöstölle.
Mitä pitää muistaa arjessa?
Osa tehtävistä vaatii listausten pitoa tietoturvan ydinelementeistä.
Mistä pitää voida raportoida?