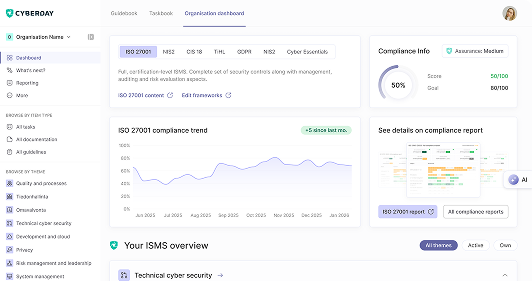
Build your ISMS in minutes, not months.
.svg)
.svg)
.svg)

Denmark’s Cybersikkerhedsloven implements NIS2 across both general critical sectors and — through a separate act — the telecom sector, introducing requirements for risk management, incident reporting, and regulatory supervision. Run the NIS2 Denmark assessment to evaluate your compliance readiness.



Vaatimukset täyttyvät jalkauttamalla digiturvatehtäviä.
Mitä kukin tekee digiturvan eteen?
Osa tehtävistä vaatii asioiden ohjeistamista henkilöstölle.
Mitä pitää muistaa arjessa?
Osa tehtävistä vaatii listausten pitoa tietoturvan ydinelementeistä.
Mistä pitää voida raportoida?