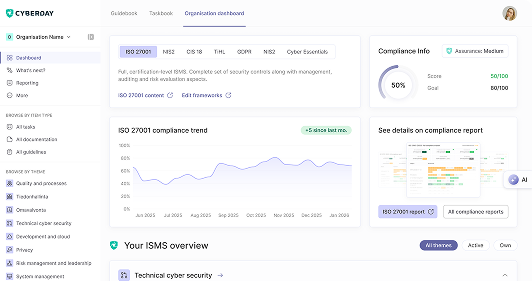
Build your ISMS in minutes, not months.
.svg)
.svg)
.svg)

China’s Cybersecurity Law defines security obligations for network operators and service providers, including personal information protection, critical infrastructure security, and data localization requirements. Take the CSL assessment to identify how your China operations align with the law’s requirements.



Vaatimukset täyttyvät jalkauttamalla digiturvatehtäviä.
Mitä kukin tekee digiturvan eteen?
Osa tehtävistä vaatii asioiden ohjeistamista henkilöstölle.
Mitä pitää muistaa arjessa?
Osa tehtävistä vaatii listausten pitoa tietoturvan ydinelementeistä.
Mistä pitää voida raportoida?